Kafka Outbound Events / Signal - Config
Outbound Events (Signals) push real-time notifications to external systems when changes occur in your IndyKite environment.
This configuration sets up event streaming to Kafka (Confluent) for configuration changes:
1. Define Confluent as the event provider.
2. Route configuration change events to a Kafka topic.
3. Receive messages when any configuration is created, read, updated, or deleted.
Use case
Scenario: You need to audit or react to configuration changes in your IndyKite project.
Each time a configuration node is modified (create, read, update, delete), an event is sent to your Kafka topic. This enables:
- Audit logging of all configuration changes.
- Triggering downstream workflows when configurations are updated.
- Real-time monitoring of your IndyKite environment.
Note: Only one Outbound Events configuration can be active per project.
Requirements
- ServiceAccount credentials created in the IndyKite Hub for your organization.
- A Confluent Cloud environment with a valid API Key.
- A Kafka topic created in your Confluent environment.
Steps
1. Create a topic in your Confluent environment to receive events.
2. Apply the Terraform configuration to create the Outbound Events setup.
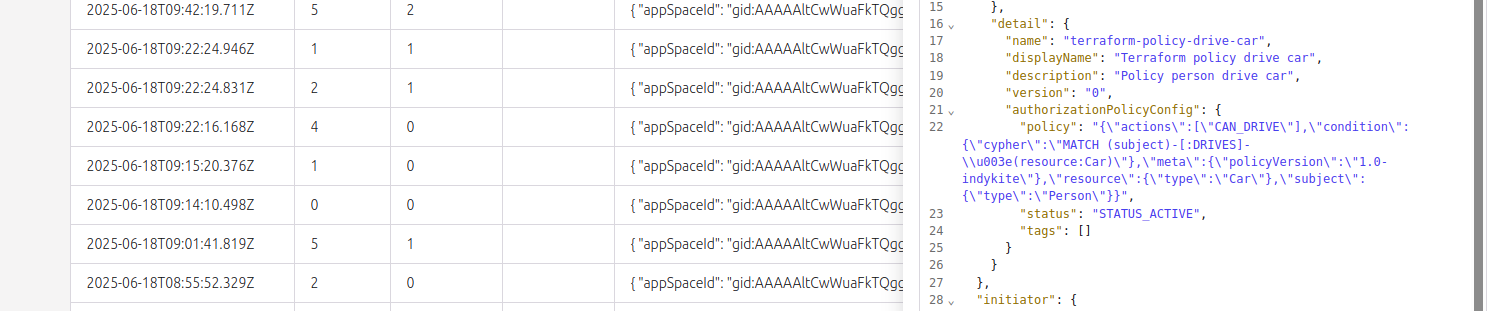
3. Perform any CRUD action on a configuration node in your project.
4. Verify that event messages appear in your Kafka topic.
terraform {
required_providers {
indykite = {
source = "indykite/indykite"
version = 1.34. # or latest version
}
}
}
# indykite provider integrates IndyKite platform with Terraform scripting.
# Provider for now does not support any parameters and all is set within service account credential file.
provider "indykite" {}
resource "time_static" "example" {}
resource "indykite_event_sink" "outbound_events" {
name = "outbound-events"
display_name = "Outbound Events"
location = "project_id"
providers {
provider_name = "confluent-provider"
include_cdc_events = false
kafka {
brokers = ["broker"]
topic = "topic_signal"
username = "api_key"
password = "api_key_secret"
}
}
routes {
provider_id = "confluent-provider"
stop_processing = true
keys_values_filter {
event_type = "indykite.audit.config.*"
}
route_display_name = "Configuration Audit Events"
route_id = "config-audit-log"
}
# lifecycle {
# create_before_destroy = true
# }
}
resource "indykite_authorization_policy" "policy_drive_car" {
name = "terraform-policy-drive-car"
display_name = "Terraform policy drive car"
description = "Policy person drive car"
json = jsonencode({
meta = {
policy_version = "2.0-kbac"
},
subject = {
type = "Person"
},
actions = ["CAN_DRIVE"],
resource = {
type = "Car"
},
condition = {
cypher = "MATCH (subject)-[:DRIVES]->(resource:Car)"
}
})
location = "project_id"
status = "active"
}